Tech giant Google has released Chrome 80, and many are wondering what disruption this may cause to the affiliate industry.

On February 4th, Google released an update to the Chrome browser known as Chrome 80 to prevent security issues caused by cookie vulnerabilities - a positive step for online security but some have voiced concerns on what this update means for the affiliate industry.
In short, the industry moves on and continues, business as usual. In mid-2019, this update was announced by Google. Unlike the bullying approach taken by Apple with its Intelligent Tracking Prevention, Google is taking a more considered and consultative approach to future updates. After all, it is their revenue at stake too when it comes to sweeping, disruptive changes in the ad tech industry.
The feature being added to the popular browser was to prevent security issues in cookie vulnerabilities. By enforcing a secure-by-default cookie classification, Google hopes to increase security and privacy in their browser and prevent potential exploitation of its users.
The core purpose of Chrome 80 is to suppress cookies from unsecured domains (you will see this in your browser where a website address begins with HTTP) as well as cookies from domains that differ to the web page domain.
In the world of affiliate marketing (and many other advertising tracking platforms) where the entire premise is redirecting traffic from one domain to another through affiliate links, you can see how this had some people concerned. Moving between domains was the whole premise of the industry and the potential of cookie-based tracking disrupted, could have lead to lost sales and a loss of measurement.
The Technical Stuff
Advertisers or eCommerce sites typically integrate external services for advertising, attribution, analytics, content recommendations and social embeds and sharing functionality. As users browse these eCommerce sites, the external services integrated may store cookies in the users' browser. These services may then subsequently access the locally stored cookies to deliver a more personalised experience or measure audience engagement for the purpose of analytics.
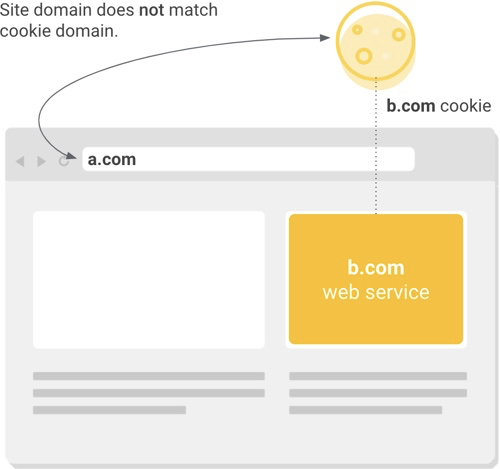
Every cookie stored on the users' computer has a domain associated with it. If the domain associated with a cookie matches an external service and not the website in the user's address bar, this is considered a cross-site (or "third party") context. It's this third-party context that has been the victim of recent changes to many browsers and privacy enhancements.
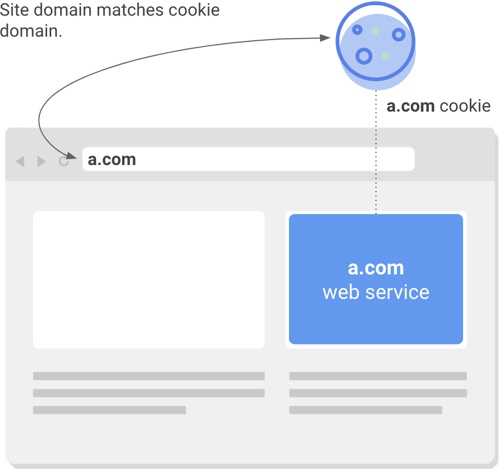
Cookies accessed in a same-site (or "first party") context occurs when the cookie's domain matches that of the website domain in the user's address bar. These Same-site cookies are commonly used to keep people logged into individual websites, remember their preferences, support site analytics and form a large part of the usability of the internet we know today.
Before the change rolled out on February 4th, if a cookie's original intent was to be accessed within a first-party context, the developer had the option to apply one of two security settings (SameSite=Lax or SameSite=Strict) to prevent external access. Although historically, very few developers followed this practice, regardless of whether it was highly recommended. Subsequently, this has left a large number of same-site cookies potentially exposed to threats.
As of February 4th and as a means to safeguard more websites and users, the new "secure-by-default" model and update to Chrome 80 enforces the rule that all cookies (unless otherwise specified) should be protected from external access. This is where the new cookie setting, SameSite=None comes into play to designate cookies for cross-site access. When the SameSite=None attribute is present in a cookie, an additional Secure attribute must also be used so that cross-site cookies can only be accessed over HTTPS/SSL connections. Like all security updates, this won't mitigate all risks associated with cross-site access, but it enhances protection against network attacks.
Will Chrome 80 effect Commission Factory Affiliates?
Being massive advocates of secure web standards, Commission Factory have been "HTTPS Everywhere" since 2013 and all of our tracking links generated through either the Platform or the API use HTTPS. Furthermore, we have been automatically redirecting any and all HTTP traffic to HTTPS since 2014.
This means that all traffic running through the Commission Factory network will not face any disruption to measurement or tracked transactions. In fact, with all of the recent updates to Apple ITP in recent months, our tracking capabilities and our adherence to these new standards or practice have only made our capabilities stronger, more robust and future-proofed.
Whilst we have the measures in place to ensure sales and measurement are all tracked accurately, for any Advertisers or Publishers that are not using secure protocols we would highly advise this is implemented and your site is secure and running through HTTPS/SSL. Sites under SSL has also been a ranking criteria in Google search since 2014 when they announced a preference for secure sites would be added to their algorithm and would provide a "lightweight" rankings boost.


